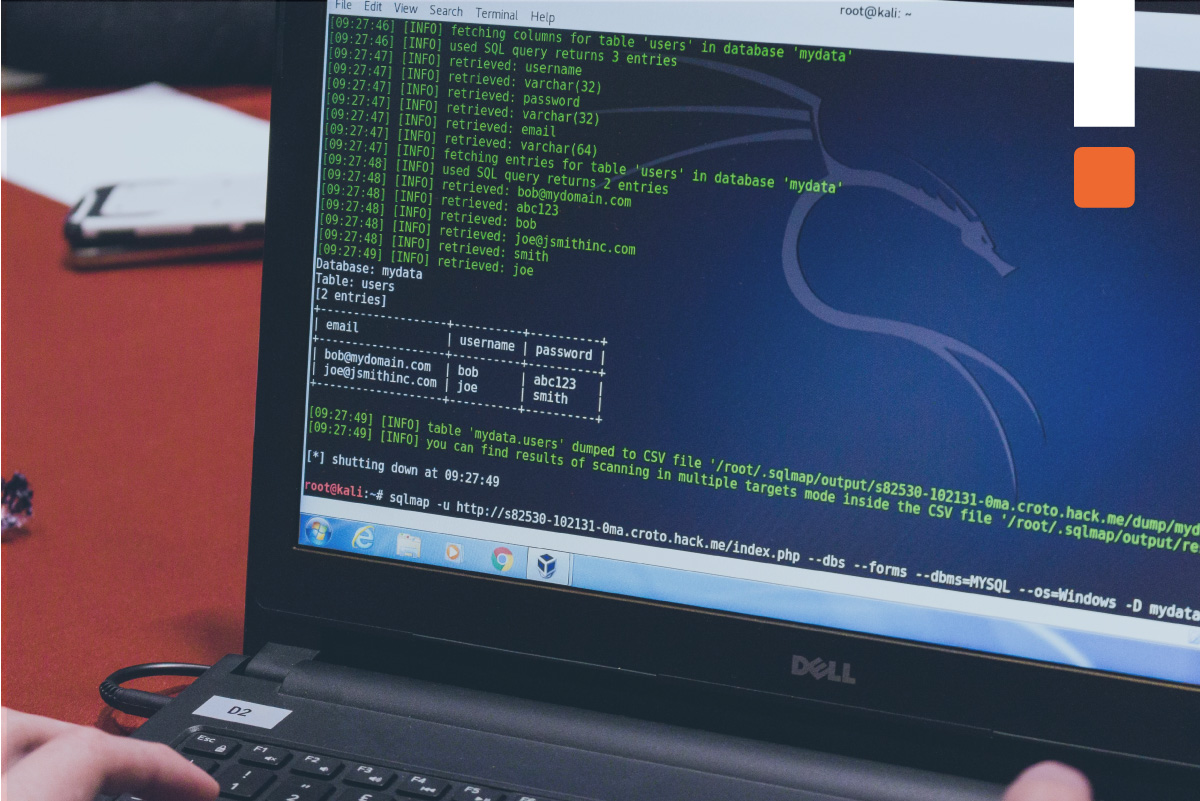
Infastruttura di laboratorio virtualizzata che prevede 6 macchine così organizzate: 2 macchine Windows server, 3 macchine client e 1 macchina d’attacco linux con Parrot OS. Di seguito una elenco dei principali software di hacking utilizzati all’interno degli oltre 150 laboratori previsti: Nessus, GFI LanGuard, CGI Scanner Nikto, Responder, L0phtCrack, Armitage, TheFatRat, Meterpreter, Power Spy, Spytech SpyAgent, OpenStego, Covert_TCP, Auditpol, CClearner, njRAT RAT, ProRat, RAT Trojan, JPS Virus Maker Tool, Low Orbital Cannon, PhoneSploit, Quixxi, lazys3, S3Scanner, HashCalc, MD5 Calculator, HashMyFiles, CryptoForge, BCTextEncoder, RMail, VeraCrypt, BitLocker Drive Encryption, Rohos Disk Encryption, CrypTool, AlphaPeeler, Netcraft, SherLock, theHarvester, Central Ops, Web Data Extractor, HTTrack, ceWL, eMailTrackerPro, DomainTools, DNSRecon, Recon-ng, Maltego, OSRFramework, BillCipher, OSINT Framework, Nmap, Angry IP Scanner, MegaPing, NetScanTools Pro, Hping3, Wireshark, Unicornscan, Colastoft Packer Builder, Network Topology Mapper, Metasploit, NetBios, SNMP-check, SoftPerfect Network Scanner, AD Explorer, OpenVAS, VirusTotal, BinText, PE Explorer, Dependency Walker, IDA, OllyDbg, TCPView, CurrPorts, Process Monitor, Rgshot, jv16 PowerTools, SrvMan, WinPatrol, Mirekusoft Install Monitor, PA File Sight, DriverView, Driver Reviver, DNSQuerySniffer, macof, arpspoof, Yersinia, Caine e Abele, TMAC e SMAC, Pmnipeek Protocol Analyzer, Steel Centeral Packet Analyzer, Xarp, Netcraft, PhishTank, OhPhish, hping3, HOIC, LOIC, Anti DDos Guardian, Zed Attack Proxy, bettercap, Snort, ZonaAlarm, HoneyBOT,Ghost Eye, Skipfish, httprecon, Netcat, Telnet, Nmpa Scripting Engine, Uniscan, Dictionary Attack, WhatWeb, OWASP ZAP, Vega, Burp Suite, Weevely, Sqlmap, DSSS, Aircrack-ng, Parrot Security, Social-Engineer Toolkit.